| THE IT SECURITY PROFESSIONAL |
Barlowtek
The It security Pro
Helping Organizations Understand IT Security
&
Best Practices
The Rogue EmployeeWe have all met those technical people that have worked for our companies that have kept to themselves and may have had some sort of run in with management, and now they want to get back at the company. How do we as IT Security Professionals protect against this threat? How do we identify if one of our own turns rogue? Security ControlsWhile most of us implement security controls for the protection of the company or business as a whole, we have to keep in mind that there are those that will try to circumvent those controls. Here are the top areas that you should be looking at to tell if an employee has gone rogue:
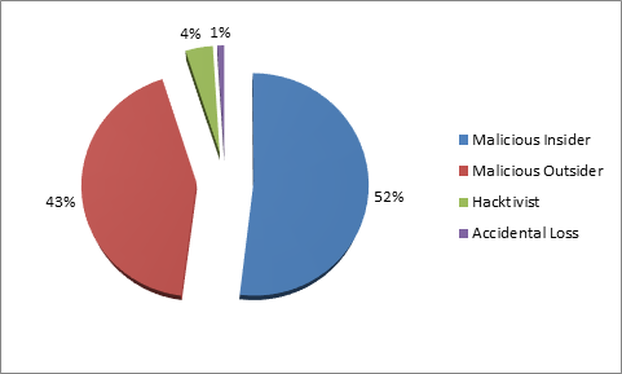
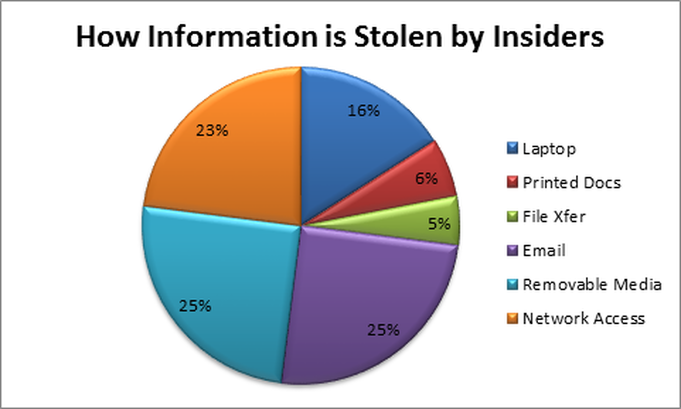
Motivations Motivation may be hard to determine for a potential insider threat. With so many variables, it may be hard to tell if it is one or multiples of reasons for it to happen. Employees that know the systems like Administrators may be the core focus of your efforts for monitoring. Nevertheless, the average user may also have motivations in which they want to capitalize on. If a user has a particular ax to grind against the business, then they may need to be watched more than others due to their proclivity towards having ill will towards the company. This should be an area that is discussed with the HR Manager or others to determine the type of impact that may happen if it is suspected. With that in mind, taking action against a potential threat may be more prudent than waiting to see if something else happens. Out for Themselves When being an IT Security Professional, it is important that you are a student of human behavior and that you understand human motivations. Whether it is designing a monitoring program or teaching new users the ins and outs of social media security. You will be called upon to determine if someone is a possible threat to your organization. However, how do you know it isn’t something about the user taking work home with them? While the motives of those that will undermine a company or business that they work for may be varied. It is important to keep in mind; our job is to protect the company we work for. Looking for the signs and behaviors of our fellow co-workers may be one of the hardest aspects of our job. Helping someone out is one thing, but helping them exfilarate data out of the business is another. Monitoring Internal Threats While we have a need to monitor our networks and those that use them. We also have to protect our businesses from all threats that may take advantage of possible cracks in our controls. The internal threat is the most impactful and the most significant threat that we face today. Countless times over the last few years we have seen rogue user exfiltration of controlled data or information. While most would agree that there is never a good reason to have organizational data leaked to the public. It is important to remember that these rogue users are usually breaking the law by transferring this information out of the business, or are breaking the security policies that they said that they would uphold when they were hired. Monitoring everyone on the network and scrutinizing every action or inaction would tie up resources. Automated Monitoring Automation has enabled the IT Security Professional to be able to monitor the network and follow up with suspicious incidents when they occur. This can be accomplished with the use of a Data Loss Protection (DLP) solution that monitors the content of information that moves across or out of the network. The key to this solution is that it is actively monitored and that incidents are followed up and addressed when they happen. While behavior may be a dead giveaway, it may be difficult to detect by managers or supervisors if they have not encountered a similar situation in the past. This is where the automated monitoring of data moving across the network will be helpful. This will provide a trail that the network admins can look at and determine if the information that is leaving the network has been authorized or if it is out of character for the user. Potential Loss
When it comes to an internal threat, the most impact that they will have will be on the loss of proprietary intellectual property (IP) that they had access to. The loss of this data may potentially affect the company in ways that can’t be directly determined, but if your company is developing a product or service that others are not, then you have a need to control this data. If the business loses the IP they have been working on, the business may end up losing out to a competitor. Just like any other risk that a company may encounter, the loss of data will have a cost associated with it. Whether it is the loss of the work done by the employee, which they took with them, or the IP that they employee helped developed. The company has already invested that money in the product or services that the employee had a help in producing. The loss here is due to the impact that it may have on the future of the company. Loss may be hard to calculate, but the impact could be devastating, especially to a small business or start-up. Summary While we take a look at the whole picture when assessing the security posture of our companies. Sometimes the hardest to see is what is in the mirror. Insider attacks account for a great deal of the costs associated with being compromised. No matter what the motivation is for the user to exfiltrate information out of the network, it happens. Whether it is done on purpose, or on accident, the impact may still be the same. It is important that the IT Security Professional to look at all threats to the business and take the needed steps to help prevent them. Note: The actions that I describe here are based on observation and coordinating efforts with others within the organization. Please contact your legal counsel to determine the right course of action and to protect the company from any legal ramifications. In addition, establishing a policy with how these types of situations arise may help to negate any sort of legal liability to your business as well.
0 Comments
Your comment will be posted after it is approved.
Leave a Reply. |
IT Security ProSecuring the future one byte at a time! Mr. Barlow is here, staying ahead of the curve in Information Security Leadership. Ready to help your company stay safe and secure. Categories
All
Archives
January 2023
|

 RSS Feed
RSS Feed